The pandemic caused by COVID-19 has a destructive reach that goes beyond that of a highly contagious and deadly illness. It is also contributing to the rapid spread of piracy — as in spreading illegal copies of commercial software.
Software piracy involves much more than businesses and consumers using illegal copies of computer programs. What lurks within the pirated copies is often rogue code — malware — that can be just as deadly to computers and users’ finances.
Software companies are reporting that piracy has increased 20 to 30 percent due to COVID-19 and working from home, according to Ted Miracco, CEO of compliance and licensing management firm Cylynt.
The Software Alliance (BSA), research shows nearly 40 percent of all software used worldwide is not properly licensed and software companies are losing nearly US$46 billion a year due to unlicensed use,” he told the E-Commerce Times.
More specifically, pirated software has a five-pronged consequence that its victims discover only when caught or infected, noted Miracco:
1. Remote work environments are creating a situation where hackers can breach an online fortress to seize a company’s intellectual property.
2. Unemployed workers are buying pirated software over the Internet to generate income.
3. WFH employees are making illegal copies of the software they need for their jobs.
4. The ubiquity of the Internet and the wholesale move to cloud computing are not as secure as they could be.
5. Software pirates and hackers are resourceful at hiding their identities and evading anti-piracy technologies.
The practice of pirating software — illegally using and distributing someone else’s software — has existed since the advent of commercial software. In most cases, pirating software involves the intentional bypass of software security controls, like licenses and entitlements, meant to prevent unauthorized use, according to Paul Dant, vice president for product management of security at Digital.ai. Dant is a reformed child hacker and former software pirate.
Worldwide Reach
Software piracy is so widespread that it exists in homes, schools, businesses, and government offices. Software piracy is practiced by individual PC users as well as computer professionals dealing wholesale in stolen applications, according to BSA.
The Software Alliance, headquartered in Washington, D.C. with operations in more than 30 countries, is an international organization representing the leading software developers and a foremost advocate for the global software industry before governments and in the international marketplace.
It generally issues a Global Software Report every two years. The last such report was published in 2018. That report found the use of unlicensed software, while down slightly over the previous two years, was still widespread. Unlicensed software is still used around the globe at alarming rates, accounting for 37 percent of software installed on personal computers — only a two percent drop from 2016.
CIOs reported unlicensed software was increasingly risky and expensive. Malware from unlicensed software cost companies worldwide nearly $359 billion a year. CIOs disclosed that avoiding data hacks and other security threats from malware was the number one reason for ensuring their networks were fully licensed.
“Software piracy and cyberattacks continue to escalate, and so far the government has done little to protect its own programs, let alone the private sector,” Miracco said. “Software companies need to take action and arm themselves with the best technological antipiracy solutions available to remain competitive and protect their assets.”
Software Piracy Hotspots
China, whose industrial output now exceeds that of the U.S., and whose policies encourage the theft of foreign technology and information, remains the world’s principal IP infringer. Other leading offenders include India and Russia, according to Miracco.
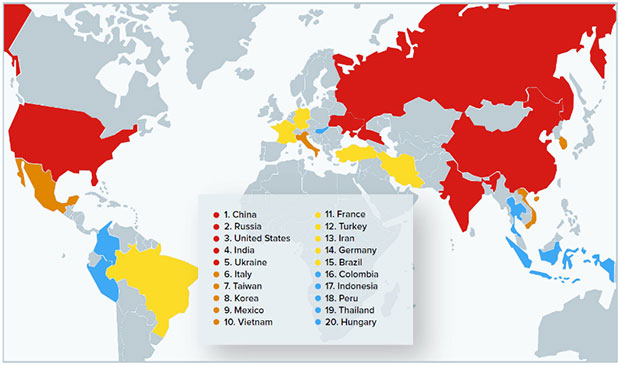
A report published by Revenera (formerly Flexera Compliance) helps companies find and mitigate security and license compliance issues, according to its website. The graph below shows its ranking of the world’s top 20 license misuse and policy hot spots.
Some compliance companies specialize in helping enterprise software users voluntarily comply with commercial software licensing requirements. Other firms seek out illegal software users. BSA and other organizations in recent years took uncooperative offenders to court to pay up.
Globally, 37 percent of business users are not paying for software, making it a $46.3 billion problem. But eighty-three percent of these unlicensed users in mature markets are legally-inclined victims of software piracy who will pay for software, according to Revenera.
The company also claims that the commercial value of unlicensed software in North America and Western Europe was $19 billion. The rest of the world totaled $27.3 billion last year.
What Drives Piracy?
The number one reason for software piracy is the cost of software licenses, according to Cylynt’s Miracco, followed by not seeing a reason to pay for something that is available free or at a cheaper price.
“In developing countries such as China, where the time and cost of developing high technology software from scratch is a barrier to leapfrogging the technology gap, the government encourages the theft of software,” he said. “This is done to reach its goal of Made in China 2025 to make China the global leader in high-tech manufacturing by 2025.”
In addition to deliberate software piracy, significant revenue is lost by software companies through unintentional misuse of licenses. Especially in today’s WFH environment, employees are sharing licenses and/or downloading cheaper, illegal software not provided by their employers on their home computers, Miracco noted.
Consider this scenario as a check of your own potentially illegitimate software use, suggested a Cylynt representative. It helps understand the path software users follow — sometimes unknowingly — to piracy.
You download software to help with a project.
Did the software come from the company or a certified partner? Or, did it come from what seemed like a legitimate free download site?
If this is the case, did the original software manufacture put its software on the site or give permission for it to be freely downloaded?
If not, you could be in violation of the software owner’s copyright. Or worse. It could be an unlicensed, pirated copy of the software full of malware about to set off a chain reaction within your company’s IT network.
Part of the Problem or Hapless Victim?
Given the above example, are software “borrowers” complicit or innocent of piracy? Software users caught in the above situation become both, in Miracco’s view.
Deliberate pirates, especially hackers from China, are encouraged by the government to steal software. In other cases, smaller companies that cannot afford to pay for expensive software buy illegal copies and provide them to their employees, who use whatever tools they are given in order to do their jobs, he reasoned.
“Sometimes, the use could be inadvertent. A WFH employee desperately needs a vital software tool and pulls it off the web without realizing it is a hacked or illegal copy,” he said.
The Piracy Scheme
Software attackers reverse engineer the target software. They identify the areas of code that handle the security controls. Then they simply modify that code to bypass or disable them, according to Digital.ai’s Dant.
“In other words, if I have your software, I can understand how it works and modify it to run completely under my control to include communication with your backend application servers. Without the appropriate protection in place, these attacks are trivial to carry out for an experienced software pirate,” he told the E-Commerce Times.
Remember Dant’s background as a reformed child hacker and former software pirate. He says this with great authority.
“We continue to struggle with software piracy today because the same inherent software exposures I utilized in the 80s and 90s still exist in plain sight,” he asserted.
“Particularly in the age of mobile apps and IoT devices, the stakes go well beyond financial loss due to software piracy. If an application is compromised, we are now contending with everything from massive data exfiltration to degraded operations in healthcare facilities to threats against our privacy, safety, and health,” he said.
Is Piracy a Problem Without a Workable Solution?
Absolutely not, retorts Miracco. Software developers who have adopted antipiracy and license compliance software and have built robust programs are satisfied with the results.
Some companies have opted to develop their own in-house programs. However, most have found that partnering with a company that specializes in antipiracy technology is less resource intensive and yields more, and higher quality, results.
“Some piracy will always exist, of course. For companies using antipiracy technology, the losses have declined sharply,” he said.
Dant has a different approach to solving the problem. Software makers must make their software more difficult to reverse engineer. They need to enable their software to detect tampering and prevent further execution in a tampered state.
“While rarely mentioned in media coverage, it is those distinct exposures that provide an attacker with an initial advantage for researching and formulating attacks surreptitiously and anonymously. But, keep in mind that developers are not meant to address these concerns,” he added.
There’s no coding trickery to fix this, Dant cautions. Protection against this type of attack relies upon establishing continuous integration and delivery pipelines that instrument protection before release, transparent to developers, and without any disruption to release flows.
An Apt Solution
Nothing is ever completely secured, especially software, Dant offered. But if software companies focus on software protection that frustrates and deters the types of attacks that enable piracy (and beyond), that effort can effectively eliminate a substantial subset of potential attackers due to their lack of necessary technical skills and motivation.
Hackers’ and pirates’ motivations vary wildly. But they are often financial in nature. The better protected your software, the more likely an attacker will choose to move on and find a less protected application that requires fewer resources to attack, Dant suggested.
“Severely diminishing the attacker’s return on investment is an effective risk mitigation strategy that can reduce the occurrence of piracy and other attacks against your software,” he concluded.














































Social CRM
See all Social CRM